This is a list of posts with tags Cyber Security
Sinkclose Vulnerability: Definition, Causes, Impacts, and How to Overcome It
Sinkclose vulnerability is a security hole that can be exploited by attackers to take control of a system, steal data, or cause damage to applications. Although …
What are the Popular Metasploit Payload Modules that Hackers Often Use?
Metasploit is one of the most popular penetration testing frameworks in the world that is widely used by cybersecurity professionals and also by hackers to …
CVE-2024-55556: Full Analysis, Impact, and Mitigation
CVE (Common Vulnerabilities and Exposures) is a system for identifying security vulnerabilities in software used worldwide. One of the latest vulnerabilities …
CVE-2024-30038: Full Analysis of Win32k Vulnerability and How to Fix It
In May 2024, Microsoft released information about a new, fairly serious security vulnerability, namely CVE-2024-30038. This vulnerability was found in the …
CVE-2024-30085: Privilege Escalation Vulnerability in Windows Cloud Files Mini Filter Driver
In 2024, a critical security vulnerability identified as CVE-2024-30085 was discovered in the Windows operating system. This vulnerability allows attackers to …
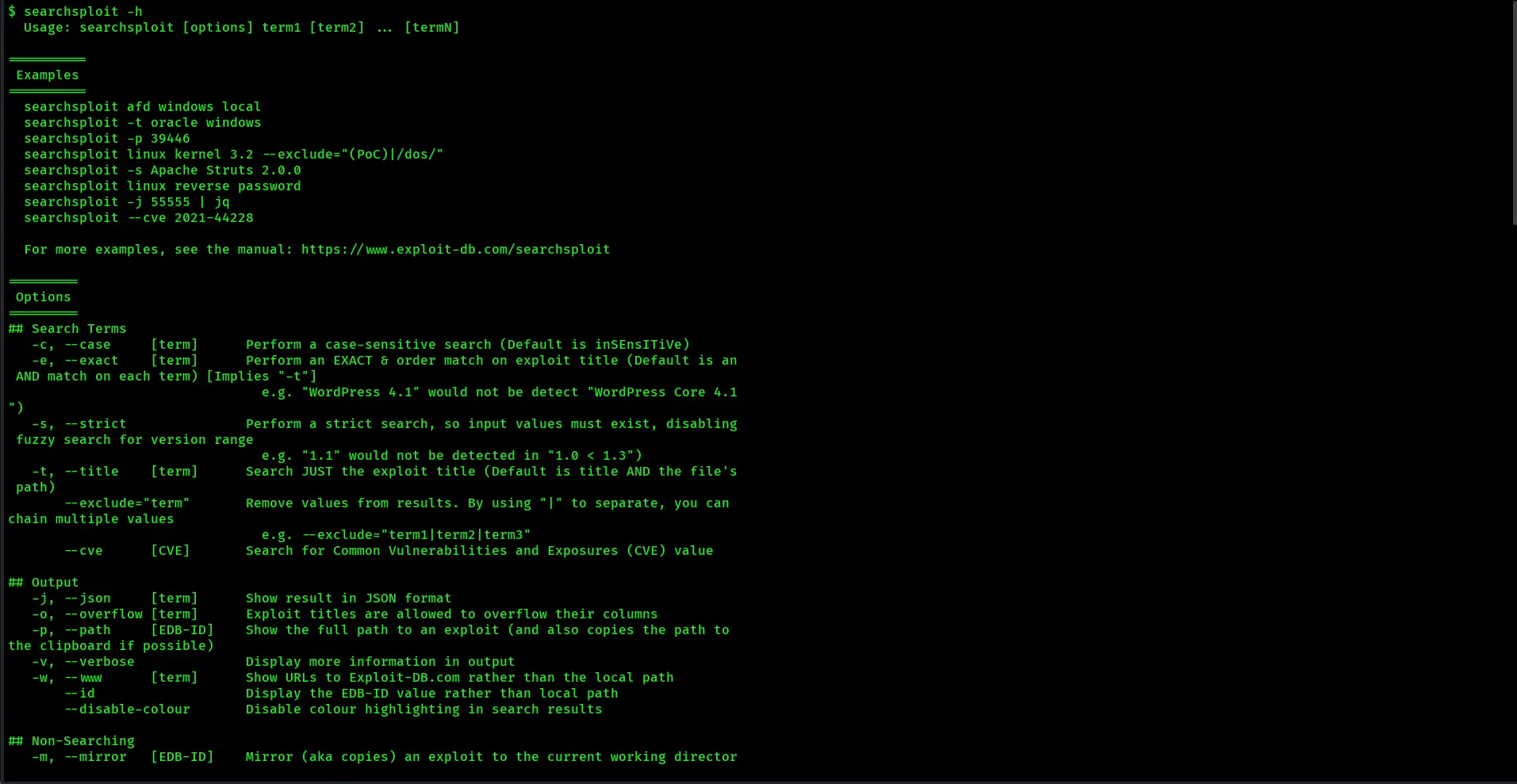
How to Use SearchSploit on Kali Linux: A Complete Guide for Beginners and Professionals
SearchSploit is one of the most useful tools in the world of cybersecurity, especially for penetration testers and ethical hackers. This tool allows users to …