New Post

Programming Logic Often Used on Online Gambling Websites
Syukra
In today’s digital era, the development of websites that provide online gambling and gaming services is increasingly rapid. Many aspects of programming …

Most Dangerous Ransomware Virus Types
Syukra
Ransomware is a type of malware that encrypts user data and demands a ransom to restore access to that data. Ransomware has become a serious cyber threat, with …

Most Dangerous Types of Malware Viruses
Syukra
In today’s digital world, viruses and malware are a real and serious threat to internet users. Here are some of the most dangerous types of viruses and …
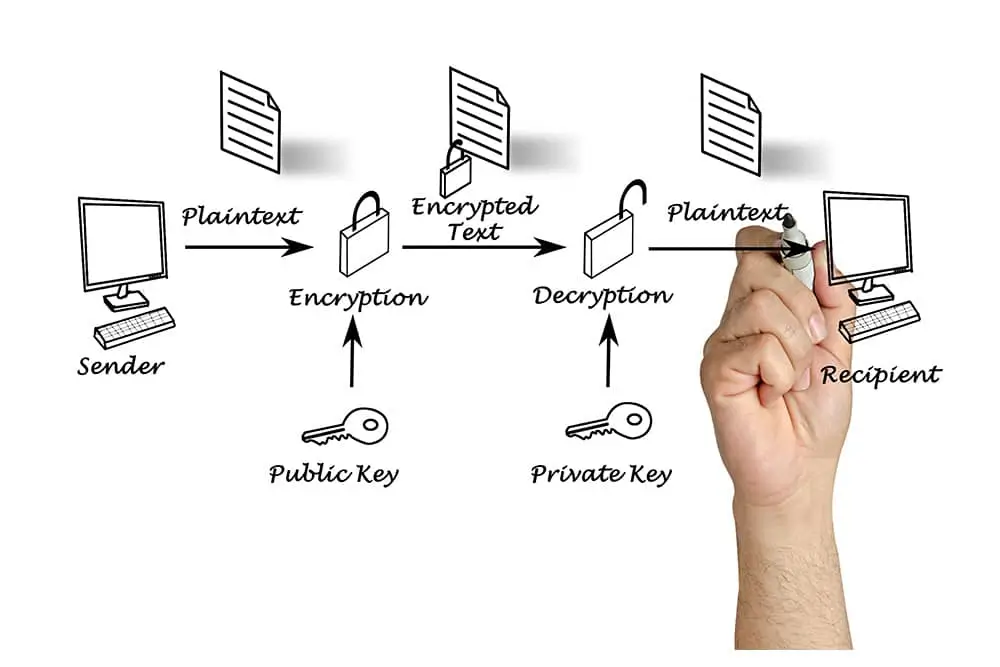
Types of Security Encryption: Definition, How It Works, and Examples
Syukra
Encryption is a data security technique that aims to protect information so that it can only be accessed by authorized parties. In today’s digital world, …

Best Antivirus Types Today
Syukra
In the increasingly advanced digital era, it is important for us to protect our devices from cyber threats. Antivirus is a crucial tool in keeping our personal …

What Are The Most Dangerous Types Of Adware?
Syukra
Adware is software that displays unwanted advertisements to users. While some types of adware are considered less dangerous, there are certain types of adware …
